Everyone using a PC will have internet. And about 75% of them is for sure to have a WiFi modem. But the thing matters is all about the speed of internet, the speed of download. If you'r jealous of your neighbors internet, and if they have a modem. Here is a hack that might come in handy all the time. Now without any more lectures, i will start explaining with steps on hacking a WiFi modem.
Using the below steps you will get the password of your neighbor or any other modem.
Lets first start with the things you need
Wireless Adapter:-
The biggest
requirement you'll need is a wireless adapter that's capable of packet
injection, there are many cards capable of injecting packets, You can
search Google for the compatibility list of WiFi Cards
I use Alfa AWUS036H which is a very popular card and it performs well with Backtrack
Back Track Live DVD/CD or USB:-
Backtrack is a Linux distro with all
the essential tools required for penetration testing , I saw a blog
which has written articles on how to make a backtrack
live CD / USB ,If your new here i would recommend you to read the
following articles to get a better understanding of what
backtrack is and how you can use it
- How to Install Backtrack - On Vmware
- How To Make a Bootable Backtrack CD / USB
Now starting with steps:-
Cracking WiFi using Backtrack:-
Step -1 Booting Backtrack
Boot your copy of Backtrack from your USB drive (refer article on how to make a bootable Backtrack USB ),Once booted you will be prompted for the login details, enter usename as "root" and password as "toor", finally enter "startx " to start backtrack .Now once you have logged in, launch a new konsole terminal by clicking the konsole terminal icon which is there on the task bar .Now plug in your Wifi usb card and type in the following commands in the terminal as shown
ifconfig wlan0 up
where wlan0 is the name of the wireless card,it can be different .To see all wireless cards connected to your system simply type" iwconfig "
Step -2 Putting your WiFi Card on Monitor Mode
The purpose of this step is to put your card into what is called monitor mode. Monitor mode is the mode whereby your card can listen to every packet in the air ,It is similar to a Promiscuous mode which is used for packet sniffing in a LAN .You can put your card into Monitor mode by entering the following commands in a terminal
airmon-ng start (your interface)
Example :- airmon-ng start wlan0
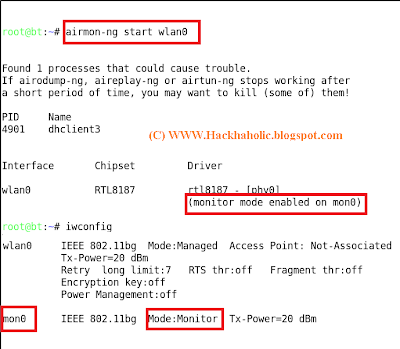
Now a new interface mon0 or ath0 will be created , You can see the new interface is in monitor mode by entering "iwconfig" as shown
Step -3 Monitor the air for WiFi Connections
Now after putting the card in monitor mode you will need to monitor the air for available wireless networks (WiFi connections)around you , For this you'll have to use a tool called "airodump" .
So you can start monitoring the air with airodump by enter the following commands
airodump-ng mon0
where mon0 is the new interface which we created in the previous step
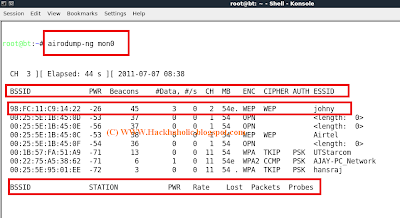
Stop the process by pressing "ctrl +c " and select your target ,Since i am only cracking WEP i will take "yashi" as my target from now on.
Step -4 Capturing Data with Airodump
Now to crack the WEP key you'll have to capture the targets data into a file, To do this we use airodump tool again, but with some additional switches to target a specific AP and channel. Most importantly, you should restrict monitoring to a single channel to speed up data collection, otherwise the wireless card has to alternate between all channels .You can restrict the capture by giving in the following commands
airodump-ng mon0 --bssid -c (channel ) -w (file name to save )As my target is broadcasted in channel 2 and has bssid "98:fc:11:c9:14:22" ,I give in the following commands and save the captured data as "johnywep"
airodump-ng mon0 --bssid 98:fc:11:c9:14:22 -c 2 -w johnywepDo not close this terminal (run the other commends simultaneously in an another terminal)
Step -5 Using Aireplay to Speed up the cracking
You will have to capture at least 25,000 data packets to crack WEP .This can be done in two ways, The first one would be a (passive attack ) wait for a client to connect to the AP and then start capturing the data packets but this method is very slow, it can take days or even weeks to capture that many data packets
The second method would be an (active attack )this method is fast and only takes minutes to generate and inject that many packets .
In an active attack you'll have do a Fake authentication (connect) with the AP ,then you'll have to generate and inject data packets.This can be done very easily by using a tool called "aireplay"
So you can do a Fake authentication with the AP using aireplay by entering the following commands in a new terminal


















0 comments:
Post a Comment